Superyacht cybersecurity: a whole of industry approach
The Atlas Cybersecurity team offer advice on how to become cyber assets and not cyber liabilities…
On day three of The Superyacht Forum 2019, the Atlas Cybersecurity team will join a number of esteemed panelists to explore current and future threats posed to superyachts and their UBOs. Herein, guest authors Eric Stride, Barry Dynkin and Benjamin Dynkin of Atlas Cybersecurity consider the cyber threat.
The superyacht industry stands at a pivotal crossroads. As cyber criminals increase their sophistication and move away from hardened targets like financial services firms, niche and high-profile industries like the superyacht industry are becoming increasingly targeted. This means that the industry, across the board, must engage in cyber risk management to ensure not only their protection, but that they can serve their function in the supply chain. In this article we hope to breakdown the threat landscape to superyachts, the industry, and offer guidance on how companies can become cybersecurity assets rather than liabilities.
I. The superyacht industry
First and foremost, it is necessary to understand the threat profile of the industry and how hackers can (and do) target it. At its core, the industry exists to serve the owners, ensuring their maximum enjoyment and minimizing any concerns, risks, or troubles they may face. We have ventured to create a breakdown of the industry and its scope:
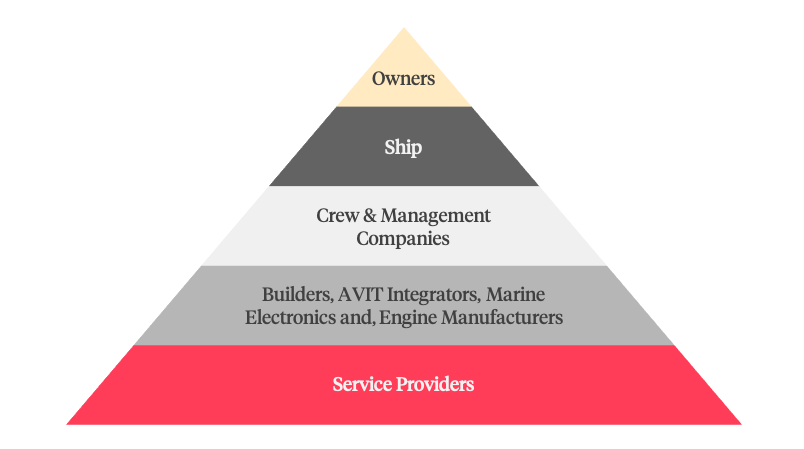
From this graphic we can see that Owners, their financial interests, privacy, and ultimately their enjoyment are the pinnacle of the industry, but in order to achieve that outcome countless other companies, individuals, processes, and systems need to work in concert. Likewise, when it comes to cyber risk management, each category is a risk that must be managed. For example, a management company may be responsible for purchasing fuel for the vessel. As such, a cybercriminal looking to steal money from an owner, may target a management company to spoof or otherwise intercept a payment for fuel. Alternatively, if a cybercriminal’s goal was real world damage to an owner, they may identify and target a security vulnerability in a navigation system or an ECIDS system and exploit that product and attack the owner through that system (i.e. spoofing a yacht’s location and causing a crash).
II. Defending against the threat and driving compliance
Understanding the landscape is an important first step because it allows for the identification of threats beyond traditional attacks. Cybercriminals are increasingly leveraging psychology, an understanding of business process, and vulnerabilities together to create sophisticated attack campaigns that are well funded, well researched, and have a remarkable success rate. In the cybersecurity industry we refer to these threats as Advanced Persistent Threats. Their campaigns can go on for months, if not years, and finding, stopping, and removing them requires the careful tuning of a robust defense strategy. The first step in any cyber defense strategy is gaining visibility and understanding the environment that needs to be defended and the threats posed by that environment. As superyachts continue to evolve in cybersecurity, it is becoming increasingly apparent that a boat cannot simply defend itself.
These principles are not simply an ad hoc recitation of best practices, but are also explicitly called out in the IMO’s cybersecurity guidance:
“Effective cyber risk management should also consider safety and security impacts resulting from the exposure or exploitation of vulnerabilities in information technology systems. This could result from inappropriate connection to operational technology systems or from procedural lapses by operational personnel or third parties” (emphasis added)
BIMCO’s guidelines are even more explicit:
“Companies should evaluate and include the physical security and cyber risk management processes of service providers in supplier agreements and contracts. Processes evaluated during supplier vetting and included in contract requirements may include:
- security management including management of sub-suppliers
- manufacturing/operational security
- software engineering and architecture
- asset and cyber incident management
- personnel security
- data and information protection.”
All this is not to say that superyachts must immediately implement enterprise-grade vendor cyber risk management, providing 100-page questionnaires, but rather superyachts, particularly in the months leading up to the January 1, 2021 deadline for implementing the IMO’s cybersecurity standard, should start understanding their supply chain, the risks that their vendors pose, and how those risks can be mitigated, both on the vessel and in their contractual relationships. In the latter, identifying, detecting, and remediating those threats requires advanced analytic capabilities; functions that require more than a ubiquitously used firewall and antivirus. Systems like Security Information Event Management, Vulnerability Management, Behavioral Analytics, and other protective and detective solutions. For the former, superyachts should begin implementing processes around BIMCO’s guidance for vendor risk management and asking risk-informed questions based on the threats posed by specific vendors. For example, the risks posed by an emergency provisions provider is fundamentally different than the risks posed by a marine electronics firm. The level of access to systems for a provisions supplier is minimal, but a marine electronics firm can have unadulterated administrator access to critical information and operational technology systems.
III. The future of cyber risk and the superyacht supply chain
As the industry continues to innovate at a breakneck pace, bringing more advanced technology onboard, the need for engaging in an industry-wide cybersecurity risk management process becomes more and more necessary. The compliance landscape has already begun to catch up with these risks, but it is incumbent, not for owners, but for vessels and those who are responsible for their administration to begin pushing the industry towards a more mature posture. There will be growing pains as service providers mature their information governance, but the industry will be better protected as a result, and superyachts and their owners will be more secure.
Remaining tickets to The Superyacht Forum 2019 are available here. Join us from 18-20 November in Amsterdam and enjoy three days of engaging workshops, thought-provoking keynotes, and interact with leading minds from our market to learn about the subjects that you and your clients need to know.
NEW: Sign up for SuperyachtNewsweek!
Get the latest weekly news, in-depth reports, intelligence, and strategic insights, delivered directly from The Superyacht Group's editors and market analysts.
Stay at the forefront of the superyacht industry with SuperyachtNewsweek
Click here to become part of The Superyacht Group community, and join us in our mission to make this industry accessible to all, and prosperous for the long-term. We are offering access to the superyacht industry’s most comprehensive and longstanding archive of business-critical information, as well as a comprehensive, real-time superyacht fleet database, for just £10 per month, because we are One Industry with One Mission. Sign up here.
Related news

Starting the journey - the next generation
A 32-year-old superyacht owner provides a candid industry SWOT analysis
Owner

DAMEN launches its first SeaXplorer
The Polar Class luxury expedition yacht is scheduled to be handed to owners in 2020
Fleet

Time to set the agenda
If boat shows are the market's shop window, TSF is the platform for strategy and agenda creation
Business

Mind your own Business
Day One of The Superyacht Forum 2019 will explore developments that will be critical to the future of your business
Business

What will the future of superyacht ownership look like?
Day two of The Superyacht Forum 2019 will explore how we must adjust to attract the next generation of owners
Owner

The future of management
How must the business of management evolve to better suit the requirements of superyacht owners?
Owner
Related news
Starting the journey - the next generation
7 years ago
DAMEN launches its first SeaXplorer
7 years ago
Time to set the agenda
7 years ago
Mind your own Business
7 years ago
The future of management
7 years ago
Tariff Wars – American Superyachts
7 years ago
NEW: Sign up for
SuperyachtNewsweek!
Get the latest weekly news, in-depth reports, intelligence, and strategic insights, delivered directly from The Superyacht Group's editors and market analysts.
Stay at the forefront of the superyacht industry with SuperyachtNewsweek




